When people imagine intelligence units, they often fall into two extremes. Some picture a lone operative with a radio, others envision analysts surrounded by screens who uncover answers with a few quick clicks. Reality sits somewhere entirely different. Modern intelligence is a collaborative system in which information is collected, shaped, tested, and re-examined through the constant interaction between analysts and operators. At Drill & Defense, this relationship is viewed as an ecosystem. Understanding how that ecosystem functions is essential for making sense of contemporary operations, whether inside a battalion-level intelligence section or a joint task structure coordinating multiple theaters at once.
Beyond the Stereotypes: Intelligence as a System
In established democracies, intelligence is defined not as improvisation but as a structured process. The U.S. Office of the Director of National Intelligence describes it as information that has been collected, processed, and analyzed to support decision-makers, placing clear emphasis on method rather than heroism. That method follows a cycle: direction, collection, processing, analysis, dissemination, and feedback. Each phase outlines how tasks flow, how priorities are set, and how intelligence is refined into something leaders can use.
The cycle is not an abstract diagram. Analysts, operators, and commanders rely on it because it organizes their responsibilities and forces them to translate broad strategic questions into manageable intelligence requirements. Direction identifies what must be understood. Collection gathers what is needed. Processing converts raw inputs into structured material. Analysis applies judgement and context. Dissemination delivers products to leaders. Feedback reshapes the next round of questions. Throughout the entire cycle, analysts and operators shape each other’s work; neither role exists in isolation.
Where Analysts and Operators Meet
Inside any functioning intelligence unit, the most important conversations occur at the beginning of the cycle. Commanders define what they need to know. Analysts translate those needs into specific, targeted questions. Operators respond with what is feasible based on the realities of the platforms, sources, or technical systems they manage.
Although this interaction is sometimes presented as linear—direction followed by collection—it is, in practice, a continuous negotiation. A signals team may clarify that certain communications networks can be intercepted while others cannot. HUMINT officers may stress that a valuable source can only be contacted under limited conditions. OSINT specialists may show that open data can illuminate certain aspects but leave other areas opaque. Analysts integrate all these constraints and still design a collection posture capable of answering the commander’s intent. That balance is where the analyst–operator dynamic becomes visible and operationally decisive.
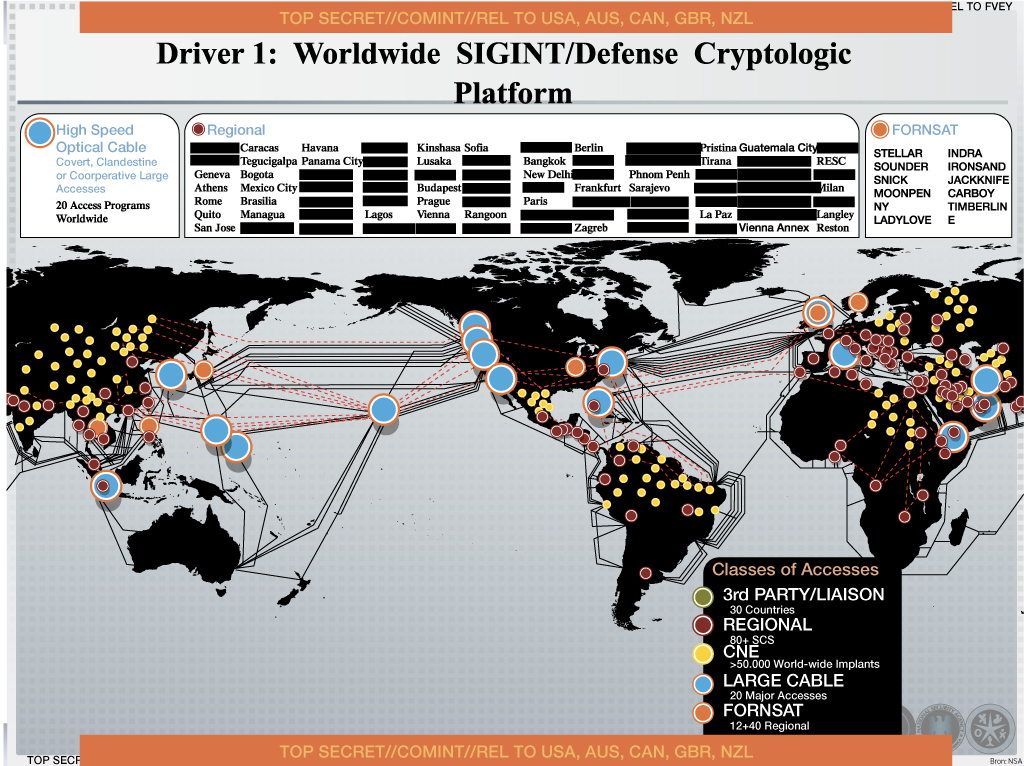
Understanding the INTs: OSINT, HUMINT, SIGINT, IMINT
The core intelligence disciplines provide the raw materials. HUMINT supplies insight into intentions and motivations through human sources, liaison relationships, and debriefings, yet must be evaluated carefully for bias or deception. SIGINT offers precise and time-sensitive access to electronic communications but depends heavily on access and capability. IMINT provides visual evidence from satellites, aircraft, and unmanned systems, though tasking priorities and environmental limits can delay results. OSINT brings in publicly available information, from media and academic analysis to commercially available satellite imagery and social-network activity; it often reveals patterns long before classified systems can respond.
Each discipline operates with its own workforce, tools, and tradecraft. Analysts are expected to understand what each can deliver and which questions each can realistically answer. The goal is not to prefer one stream but to evaluate them together, weigh contradictions, and reach a coherent assessment that acknowledges the strengths and limitations of the evidence.

Inside a Modern Intelligence Unit
Although organizational charts differ between states, modern intelligence structures are increasingly integrated. Military and civilian systems combine all-source cells, HUMINT elements, SIGINT and cyber units, imagery sections, and liaison officers who connect the organization with partners. Within this architecture, analysts and operators do not work in separate silos. Operators maintain systems, manage sources, run platforms, and execute missions. Analysts fuse incoming information, correlate it with historical data and other streams, and shape it into assessments tailored to the decisions that must be made.
The most successful units reduce the distance between these roles. Training, doctrine, and multinational exercises increasingly emphasize that analysts should understand operational constraints, while operators should understand how and why their reporting is used. NATO’s work on OSINT capability, for example, stresses that intelligence only functions when people, tools, and processes operate as one system rather than disconnected specialties.
How the System Works in Practice
Imagine a command trying to determine whether an adversary intends to disrupt a major supply route. Analysts begin by establishing a baseline using available reporting and OSINT. Imagery, traffic data, and previous incidents help define what “normal” looks like. Once this baseline exists, analysts work with collection managers and operators to gather more targeted information.
HUMINT collectors examine their sources for changes in behavior, new instructions, or coordination among armed groups. SIGINT units look for shifts in communications patterns or encrypted exchanges that might indicate planning. IMINT crews are tasked to collect imagery of suspected staging sites or transport movements. OSINT specialists review online chatter, local reporting, and commercial imagery for early signals of preparation.
As these streams converge, analysts interpret them not as isolated facts but as a pattern. A single unverified report does not trigger a warning, but alignment across multiple disciplines creates an assessment with operational weight. Commanders then receive actionable options such as rerouting traffic, reinforcing weak points, or adjusting patrol schedules. As situations evolve, the assessment is reassessed. Mistaken assumptions are corrected, and the entire cycle refines itself. The analyst–operator dynamic becomes an ongoing loop of adjustment rather than a one-time product.
Correcting Misconceptions
Public debate often reduces intelligence to simple formulas, but real units operate with far more nuance. OSINT, for instance, is not free trivia; it requires careful validation and structured tradecraft, especially in an era of disinformation and fragmented digital platforms. Operators, no matter how skilled, cannot absorb the full volume of modern data without analytical support. Likewise, automation enhances intelligence collection and processing but does not replace the judgement needed to weigh intentions, credibility, and second-order effects.
The strength of an intelligence system comes from alignment—between the commander’s intent, the analyst’s questions, the operator’s capabilities, and the feedback loop that corrects errors as missions unfold.
Why the Analyst–Operator Dynamic Matters
When intelligence fails, blame usually settles on a single role, but most failures stem from a breakdown in the relationship between analysts and operators. Unclear requirements, unrealistic expectations, poor communication, and missing feedback form the root of many high-profile intelligence problems. Conversely, when intelligence succeeds, it is often because operators understand why they are collecting what they collect, analysts remain close to mission realities, and leadership encourages continuous dialogue.
For anyone following contemporary defense and security issues, this dynamic reveals more than dramatic operations or advanced technologies. It shows how intelligence organizations actually function: as systems built on cooperation, discipline, and constant recalibration. The outcome of many modern conflicts depends not only on physical capabilities but on how effectively analysts and operators can align their roles to support a shared operational purpose.
References
- Office of the Director of National Intelligence, “What Is Intelligence?”
- Intelligence.gov, “How the Intelligence Community Works.”
- ASIS International, “Six Steps in the Intelligence Cycle.”
- U.S. Department of Defense, “Intelligence Collection Management.”
- NATO, Open Source Intelligence Handbook.
- NATO Allied Command Transformation, “OSINT Capability Requirements.”






















